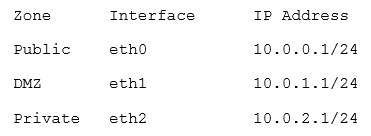
A firewall ACL is configured as follows:
10. Deny Any Trust to Any DMZ eq to TCP port 22
11. Allow 10.200.0.0/16 to Any DMZ eq to Any
12. Allow 10.0.0.0/8 to Any DMZ eq to TCP ports 80, 443
13. Deny Any Trust to Any DMZ eq to Any
A technician notices that users in the 10.200.0.0/16 network are unable to SSH into servers in the DMZ.
The company wants 10.200.0.0/16 to be able to use any protocol, but restrict the rest of the 10.0.0.0/8 subnet to web browsing only. Reordering the ACL in which of the following manners would meet the company’s objectives?
A. 11, 10, 12, 13
B. 12, 10, 11, 13
C. 13, 10, 12, 11
D. 13, 12, 11, 10