A company is adopting a BYOD policy and is looking for a comprehensive solution to protect company information on user devices. Which of the following solutions
would BEST support the policy?
A. Mobile device management
B. Full-device encryption
C. Remote wipe
D. Biometrics
CompTIA Security+ Question J-98
Which of the following is the BEST reason for placing a password lock on a mobile device?
A. Prevents an unauthorized user from accessing owner’s data
B. Enables remote wipe capabilities
C. Stops an unauthorized user from using the device again
D. Prevents an unauthorized user from making phone calls
CompTIA Security+ Question I-5
Jane, an IT security technician, needs to create a way to secure company mobile devices. Which of the following BEST meets this need?
A. Implement voice encryption, pop-up blockers, and host-based firewalls.
B. Implement firewalls, network access control, and strong passwords.
C. Implement screen locks, device encryption, and remote wipe capabilities.
D. Implement application patch management, antivirus, and locking cabinets.
CompTIA Security+ Question G-8
Which of the following is the primary security concern when deploying a mobile device on a network?
A. Strong authentication
B. Interoperability
C. Data security
D. Cloud storage technique
CompTIA Security+ Question G-5
The librarian wants to secure the public Internet kiosk PCs at the back of the library. Which of the following would be the MOST appropriate? (Select TWO).
A. Device encryption
B. Antivirus
C. Privacy screen
D. Cable locks
E. Remote wipe
CompTIA Security+ Question F-57
A bank has recently deployed mobile tablets to all loan officers for use at customer sites. Which of the following would BEST prevent the disclosure of customer data in the event that a tablet is lost or stolen?
A. Application control
B. Remote wiping
C. GPS
D. Screen-locks
CompTIA Security+ Question F-55
Which of the following would prevent a user from installing a program on a company-owned mobile device?
A. White-listing
B. Access control lists
C. Geotagging
D. Remote wipe
CompTIA Security+ Question C-7
Which of the following can be used on a smartphone to BEST protect against sensitive data loss if the device is stolen? (Select TWO).
A. Tethering
B. Screen lock PIN
C. Remote wipe
D. Email password
E. GPS tracking
F. Device encryption
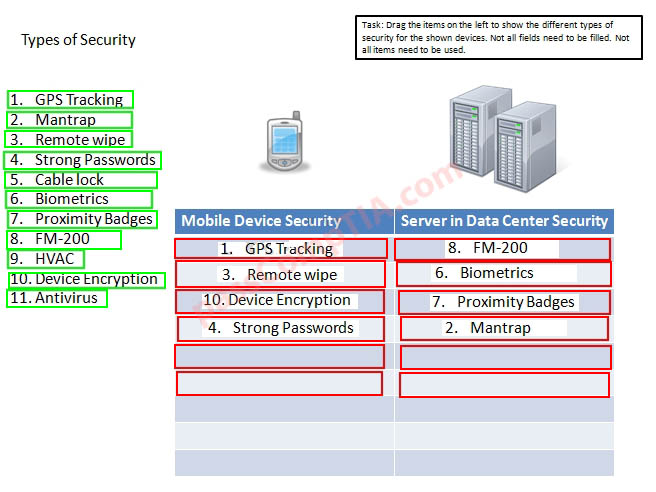
CompTIA Security+ Simulation 10
CompTIA Security+ Simulation 7
A Security administrator wants to implement strong security on the company smart phones and terminal servers located in the data center. Drag and Drop the applicable controls to each asset type.
Instructions: Controls can be used multiple times and not all placeholders needs to be filled. When you have completed the simulation, Please select Done to submit.