A security engineer must establish a method to assess compliance with company security policies as they apply to the unique configuration of individual endpoints, as well as to the shared configuration policies of common devices.
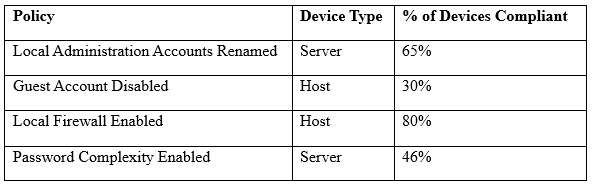
Which of the following tools is the security engineer using to produce the above output?
A. Vulnerability scanner
B. SIEM
C. Port scanner
D. SCAP scanner
CompTIA Advanced Security Practitioner (CASP) Question 39
A newly hired systems administrator is trying to connect a new and fully updated, but very customized, Android device to access corporate resources. However, the MDM enrollment process continually fails. The administrator asks a security team member to look into the issue.
Which of the following is the MOST likely reason the MDM is not allowing enrollment?
A. The OS version is not compatible
B. The OEM is prohibited
C. The device does not support FDE
D. The device is rooted
CompTIA Advanced Security Practitioner (CASP) Question 38
A hospital uses a legacy electronic medical record system that requires multicast for traffic between the application servers and databases on virtual hosts that support segments of the application. Following a switch upgrade, the electronic medical record is unavailable despite physical connectivity between the hypervisor and the storage being in place. The network team must enable multicast traffic to restore access to the electronic medical record. The ISM states that the network team must reduce the footprint of multicast traffic on the network.

Using the above information, on which VLANs should multicast be enabled?
A. VLAN201, VLAN202, VLAN400
B. VLAN201, VLAN202, VLAN700
C. VLAN201, VLAN202, VLAN400, VLAN680, VLAN700
D. VLAN400, VLAN680, VLAN700
CompTIA Advanced Security Practitioner (CASP) Question 37
A security administrator wants to allow external organizations to cryptographically validate the company’s domain name in email messages sent by employees. Which of the following should the security administrator implement?
A. SPF
B. S/MIME
C. TLS
D. DKIM
CompTIA Advanced Security Practitioner (CASP) Question 36
An organization is preparing to develop a business continuity plan. The organization is required to meet regulatory requirements relating to confidentiality and availability, which are well-defined. Management has expressed concern following initial meetings that the organization is not fully aware of the requirements associated with the regulations.
Which of the following would be MOST appropriate for the project manager to solicit additional resources for during this phase of the project?
A. After-action reports
B. Gap assessment
C. Security requirements traceability matrix
D. Business impact assessment
E. Risk analysis
CompTIA Advanced Security Practitioner (CASP) Question 35
A SaaS-based email service provider often receives reports from legitimate customers that their IP netblocks are on blacklists and they cannot send email. The SaaS has confirmed that affected customers typically have IP addresses within broader network ranges and some abusive customers within the same IP ranges may have performed spam campaigns.
Which of the following actions should the SaaS provider perform to minimize legitimate customer impact?
A. Inform the customer that the service provider does not have any control over third-party blacklist entries. The customer should reach out to the blacklist operator directly
B. Perform a takedown of any customer accounts that have entries on email blacklists because this is a strong indicator of hostile behavior
C. Work with the legal department and threaten legal action against the blacklist operator if the netblocks are not removed because this is affecting legitimate traffic
D. Establish relationship with a blacklist operators so broad entries can be replaced with more granular entries and incorrect entries can be quickly pruned
CompTIA Advanced Security Practitioner (CASP) Question 34
An agency has implemented a data retention policy that requires tagging data according to type before storing it in the data repository. The policy requires all business emails be automatically deleted after two years. During an open records investigation, information was found on an employee’s work computer concerning a conversation that occurred three years prior and proved damaging to the agency’s reputation.
Which of the following MOST likely caused the data leak?
A. The employee manually changed the email client retention settings to prevent deletion of emails
B. The file that contained the damaging information was mistagged and retained on the server for longer than it should have been
C. The email was encrypted and an exception was put in place via the data classification application
D. The employee saved a file on the computer’s hard drive that contained archives of emails, which were more than two years old
CompTIA Advanced Security Practitioner (CASP) Question 33
A forensics analyst suspects that a breach has occurred. Security logs show the company’s OS patch system may be compromised, and it is serving patches that contain a zero-day exploit and backdoor. The analyst extracts an executable file from a packet capture of communication between a client computer and the patch server.
Which of the following should the analyst use to confirm this suspicion?
A. File size
B. Digital signature
C. Checksums
D. Anti-malware software
E. Sandboxing
CompTIA Advanced Security Practitioner (CASP) Question 32
A company is acquiring incident response and forensic assistance from a managed security service provider in the event of a data breach. The company has selected a partner and must now provide required documents to be reviewed and evaluated. Which of the following documents would BEST protect the company and ensure timely assistance? (Choose two.)
A. RA
B. BIA
C. NDA
D. RFI
E. RFQ
F. MSA
CompTIA Advanced Security Practitioner (CASP) Question 31
After multiple service interruptions caused by an older datacenter design, a company decided to migrate away from its datacenter. The company has successfully completed the migration of all datacenter servers and services to a cloud provider. The migration project includes the following phases:
– Selection of a cloud provider
– Architectural design
– Microservice segmentation
– Virtual private cloud
– Geographic service redundancy
– Service migration
The Chief Information Security Officer (CISO) is still concerned with the availability requirements of critical company applications. Which of the following should the company implement NEXT?
A. Multicloud solution
B. Single-tenancy private cloud
C. Hybrid cloud solution
D. Cloud access security broker