Which of the following BEST describes the process of documenting everyone who has physical access or possession of evidence
A. Legal hold
B. Chain of custody
C. Secure copy protocol
D. Financial responsiblity
CompTIA exam questions
Which of the following BEST describes the process of documenting everyone who has physical access or possession of evidence
A. Legal hold
B. Chain of custody
C. Secure copy protocol
D. Financial responsiblity
A network administrator configures an email server to use secure protocols. When the upgrade is completed, which of the following ports on the firewall should be configured to allow for connectivity? (Choose three.)
A. TCP 25
B. TCP 110
C. TCP 143
D. TCP 389
E. TCP 587
F. TCP 993
G. TCP 995
A network technician needs to separate a web server listening on port 80 from the internal LAN and secure the server from the public Internet. The web server should be accessible to the public Internet over port 80 but not the private LAN. Currently, the network is segmented with a network-based firewall using the following IP addressing scheme on each interface:
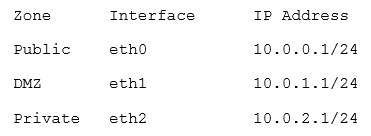
Which of the following ones should the technician use to place the web server and which of the following firewall rules should the technician configure?
A. Place the web server in the public zone with an inbound rule from eth0 interface to accept traffic over port 80 designated to the web server
B. Place the web server in the DMZ with an inbound rule from eth0 interface to eth1 to accept traffic over port 80 designated to the web server
C. Place the web server in the private zone with an inbound rule from eth2 interface to eth1 to accept traffic over port 80 designated to the web server
D. Place the web server in the DMZ with an inbound rule from eth1 interface to eth0 to accept traffic over port 80 designated to the web server
A administrator’s network has OSPF for the internal routing protocol and has two interfaces that continue to flap. The administrator reviews the following output:
Fast ethernet 0 is up, line protocol is up
Int ip address is 10.20.130.5/25
MTU 1500 bytes, BW10000 kbit, DLY 100 usec Reliability 255/255, Tx load 1/255, Rx load 1/255 Encapsulation ospf, loopback not set
Keep alive 10
Full duplex, 100Mb/s, 100Base Tx/Fx Received 1052993 broadcasts
1258 input errors
983881 packet output, 768588 bytes
1747 output errors, 0 collisions, 423 resets
Which of the following problems would cause the interface flap?
A. Wrong IP address
B. Loopback not set
C. Bad wire
D. Incorrect encapsulation
E. Duplex mismatch
Which of the following communication technologies is used by video conferencing systems to synchronize video streams, and reduce bandwidth, sent by a central location to subscribed devices?
A. Anycast
B. Unicast
C. CoS
D. QoS
E. Multicast
Network segmentation provides which of the following benefits?
A. Security through isolation
B. Link aggregation
C. Packet flooding through all ports
D. High availability through redundancy
A technician needs to ensure that new systems are protected from electronic snooping of Radio Frequency emanations. Which of the following standards should be consulted?
A. DWDM
B. MIMO
C. TEMPEST
D. DOCSIS
Which of the following protocols uses label-switching routers and label-edge routers to forward traffic?
A. BGP
B. OSPF
C. IS-IS
D. MPLS
A company has had several virus infections over the past few months. The infections were caused by vulnerabilities in the application versions that are being used. Which of the following should an administrator implement to prevent future outbreaks?
A. Host-based intrusion detection systems
B. Acceptable use policies
C. Incident response team
D. Patch management
An administrator only has telnet access to a remote workstation. Which of the following utilities will identify if the workstation uses DHCP?
A. tracert
B. ping
C. dig
D. ipconfig
E. netstat