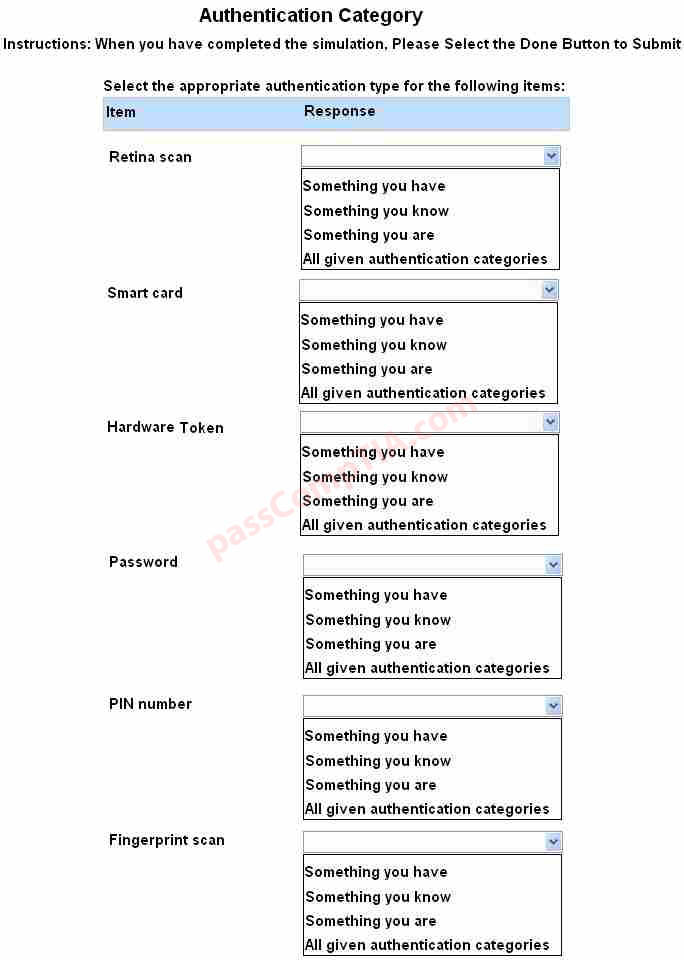
For each of the given items, select the appropriate authentication category from the drop down
choices.
Select the appropriate authentication type for the following items:
CompTIA exam questions
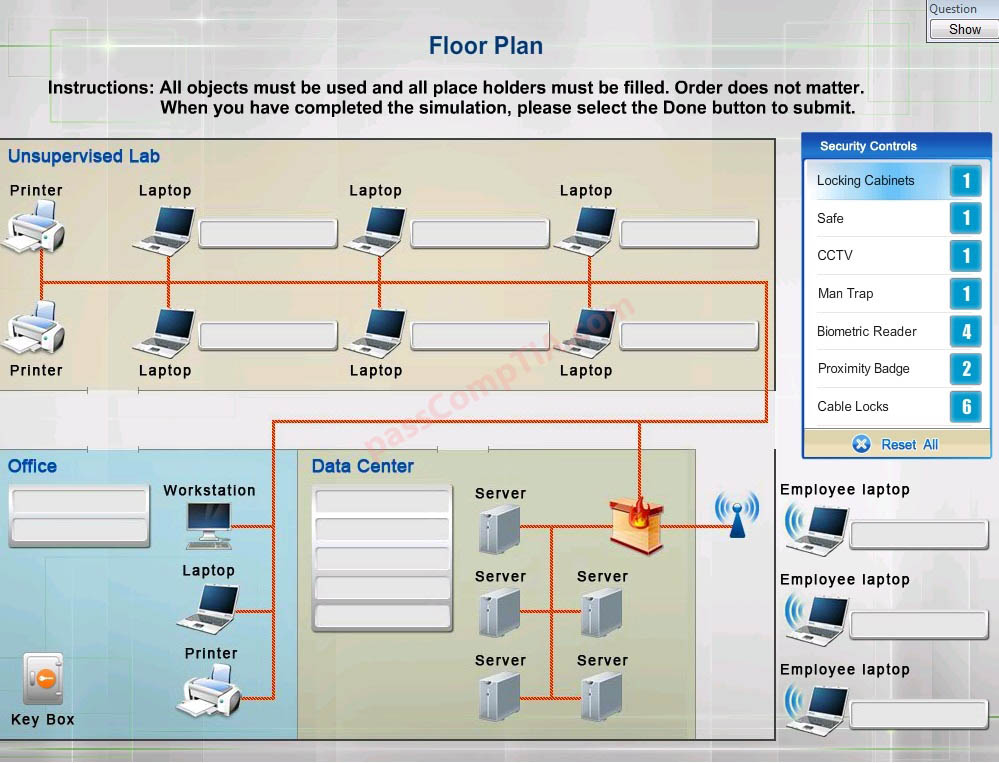
DRAG DROP
You have been tasked with designing a security plan for your company. Drag and drop the appropriate security controls on the floor plan.
Instructions:All objects must be used and all place holders must be filled. Order does not matter. When you have completed the simulation, please select the Done button to submit.
A company owns four kiosks that are in close proximity within a shopping center. The owner is concerned about someone accessing the internet via the kiosk’s wireless network. Which of the following should be implemented to provide wireless access only to the employees working at the kiosk?
A. Firewall
B. Web filtering
C. MAC filtering
D. Host-based antivirus
A network technician has been asked to make the connections necessary to add video transported via fiber optics to the LAN within a building. Which of the following is the MOST common connector that will be used on the switch to connect the media converter?
A. FDDI
B. Fiber coupler
C. MT-RJ
D. ST
Which of the following network topologies has a central, single point of failure?
A. Ring
B. Star
C. Hybrid
D. Mesh
A company plan established to resume normal system operations following a disruption in business would be described as which of the following?
A. First responders
B. User awareness training
C. Disaster recovery
D. Business continuity
A network technician receives the following alert from a network device: “High utilizations threshold exceeded on gi1/0/24 : current value 9413587.54” Which of the following is being monitored to trigger the alarm?
A. Speed and duplex mismatch
B. Wireless channel utilization
C. Network device CPU
D. Network device memory
E. Interface link status