A company wants to extend its help desk availability beyond business hours. The Chief Information Officer (CIO) decides to augment the help desk with a third- party service that will answer calls and provide Tier 1 problem resolution, such as password resets and remote assistance. The security administrator implements the following firewall change:
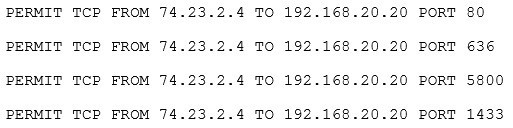
The administrator provides the appropriate path and credentials to the third-party company. Which of the following technologies is MOST likely being used to provide access to the third company?
A. LDAP
B. WAYF
C. OpenID
D. RADIUS
E. SAML
CompTIA Security+ Question L-68
Which of the following protocols is MOST likely to be leveraged by users who need additional information about another user?
A. LDAP
B. RADIUS
C. Kerberos
D. TACACS+