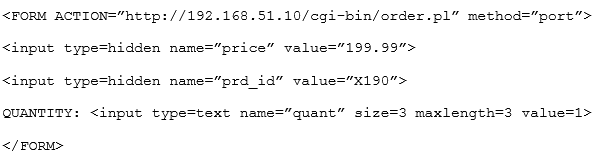
A systems administrator has installed a disk wiping utility on all computers across the organization and configured it to perform a seven-pass wipe and an additional pass to overwrite the disk with zeros. The company has also instituted a policy that requires users to erase files containing sensitive information when they are no longer needed. To ensure the process provides the intended results, an auditor reviews the following content from a randomly selected decommissioned hard disk:
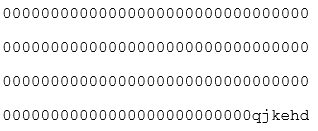
Which of the following should be included in the auditor’s report based on the above findings?
A. The hard disk contains bad sectors
B. The disk has been degaussed.
C. The data represents part of the disk BIOS.
D. Sensitive data might still be present on the hard drives.
CompTIA Advanced Security Practitioner (CASP) Question 9
A security analyst is troubleshooting a scenario in which an operator should only be allowed to reboot remote hosts but not perform other activities. The analyst inspects the following portions of different configuration files:
Configuration file 1:
Operator ALL=/sbin/reboot
Configuration file 2:
Command=”/sbin/shutdown now”, no-x11-forwarding, no-pty, ssh-dss
Configuration file 3:
Operator:x:1000:1000::/home/operator:/bin/bash
Which of the following explains why an intended operator cannot perform the intended action?
A. The sudoers file is locked down to an incorrect command
B. SSH command shell restrictions are misconfigured
C. The passwd file is misconfigured
D. The SSH command is not allowing a pty session
CompTIA Advanced Security Practitioner (CASP) Question 8
An organization is engaged in international business operations and is required to comply with various legal frameworks. In addition to changes in legal frameworks, which of the following is a primary purpose of a compliance management program?
A. Following new requirements that result from contractual obligations
B. Answering requests from auditors that relate to e-discovery
C. Responding to changes in regulatory requirements
D. Developing organizational policies that relate to hiring and termination procedures
CompTIA Advanced Security Practitioner (CASP) Question 7
A medical device company is implementing a new COTS antivirus solution in its manufacturing plant. All validated machines and instruments must be retested for interoperability with the new software.
Which of the following would BEST ensure the software and instruments are working as designed?
A. System design documentation
B. User acceptance testing
C. Peer review
D. Static code analysis testing
E. Change control documentation
CompTIA Advanced Security Practitioner (CASP) Question 6
A penetration tester noticed special characters in a database table. The penetration tester configured the browser to use an HTTP interceptor to verify that the front-end user registration web form accepts invalid input in the user’s age field. The developer was notified and asked to fix the issue.
Which of the following is the MOST secure solution for the developer to implement?
A. IF $AGE == “!@#%^&*()_+<>?”:{}[]” THEN ERROR
B. IF $AGE == [1234567890] {1,3} THEN CONTINUE
C. IF $AGE != “a-bA-Z!@#$%^&*()_+<>?”{}[]”THEN CONTINUE
D. IF $AGE == [1-0] {0,2} THEN CONTINUE
CompTIA Advanced Security Practitioner (CASP) Question 5
At a meeting, the systems administrator states the security controls a company wishes to implement seem excessive, since all of the information on the company’s web servers can be obtained publicly and is not proprietary in any way. The next day the company’s website is defaced as part of an SQL injection attack, and the company receives press inquiries about the message the attackers displayed on the website.
Which of the following is the FIRST action the company should take?
A. Refer to and follow procedures from the company’s incident response plan.
B. Call a press conference to explain that the company has been hacked.
C. Establish chain of custody for all systems to which the systems administrator has access.
D. Conduct a detailed forensic analysis of the compromised system.
E. Inform the communications and marketing department of the attack details.
CompTIA Advanced Security Practitioner (CASP) Question 4
The government is concerned with remote military missions being negatively being impacted by the use of technology that may fail to protect operational security. To remediate this concern, a number of solutions have been implemented, including the following:
– End-to-end encryption of all inbound and outbound communication, including personal email and chat sessions that allow soldiers to securely communicate with families.
– Layer 7 inspection and TCP/UDP port restriction, including firewall rules to only allow TCP port 80 and 443 and approved applications A host-based whitelist of approved websites and applications that only allow mission-related tools and sites
– The use of satellite communication to include multiple proxy servers to scramble the source IP address
Which of the following is of MOST concern in this scenario?
A. Malicious actors intercepting inbound and outbound communication to determine the scope of the mission
B. Family members posting geo-tagged images on social media that were received via email from soldiers
C. The effect of communication latency that may negatively impact real-time communication with mission control
D. The use of centrally managed military network and computers by soldiers when communicating with external parties
CompTIA Advanced Security Practitioner (CASP) Question 3
CompTIA Advanced Security Practitioner (CASP) Question 2
A company has created a policy to allow employees to use their personally owned devices. The Chief Information Officer (CISO) is getting reports of company data appearing on unapproved forums and an increase in theft of personal electronic devices.
Which of the following security controls would BEST reduce the risk of exposure?
A. Disk encryption on the local drive
B. Group policy to enforce failed login lockout
C. Multifactor authentication
D. Implementation of email digital signatures
CompTIA Advanced Security Practitioner (CASP) Question 1
A forensic analyst suspects that a buffer overflow exists in a kernel module. The analyst executes the following command:
dd if=/dev/ram of=/tmp/mem/dmp
The analyst then reviews the associated output:
^34^#AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA/bin/bash^21^03#45
However, the analyst is unable to find any evidence of the running shell. Which of the following of the MOST likely reason the analyst cannot find a process ID for the shell?
A. The NX bit is enabled
B. The system uses ASLR
C. The shell is obfuscated
D. The code uses dynamic libraries