A network administrator has been asked to install an Intrusion Detection System (IDS) to improve the security posture of an organization. Which of the following control types is an IDS?
A. Corrective
B. Physical
C. Detective
D. Administrative
CompTIA Security+ Question M-19
Which of the following should be put in place when negotiating with a new vendor about the timeliness of the response to a significant security outage or incident?
A. MOU
B. MTTR
C. SLA
D. NDA
CompTIA Security+ Question M-18
A company has drafted an insider-threat policy that prohibits the use of external storage devices. Which of the following would BEST protect the company from data exfiltration via removable media?
A. Monitoring large data transfer transactions in the firewall logs
B. Developing mandatory training to educate employees about the removable media policy
C. Implementing a group policy to block user access to system files
D. Blocking removable-media devices and write capabilities using a host-based security tool
CompTIA Security+ Question M-17
A network administrator has been alerted that web pages are experiencing long load times. After determining it is not a routing or DNS issue, the administrator logs in to the router, runs a command, and receives the following output:
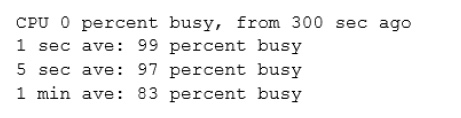
Which of the following is the router experiencing?
A. DDoS attack
B. Memory leak
C. Buffer overflow
D. Resource exhaustion
CompTIA Security+ Question M-16
A security analyst receives a SIEM alert that someone logged in to the appadmin test account, which is only used for the early detection of attacks. The security analyst then reviews the following application log:
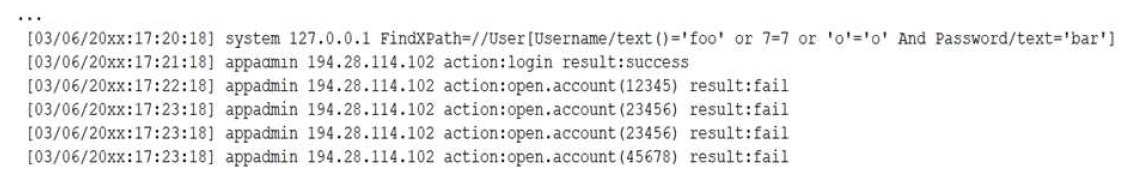
Which of the following can the security analyst conclude?
A. A replay attack is being conducted against the application.
B. An injection attack is being conducted against a user authentication system.
C. A service account password may have been changed, resulting in continuously failed logins within the application.
D. A credentialed vulnerability scanner attack is testing several CVEs against the application.
CompTIA Security+ Question M-15
A company provides mobile devices to its users to permit access to email and enterprise applications. The company recently started allowing users to select from several different vendors and device models. When configuring the Mobile Device Management (MDM), which of the following is a key security implication of this heterogeneous device approach?
A. The most common set of MDM configurations will become an effective set of enterprise mobile security controls.
B. All devices will need to support SCEP-based enrollment; therefore, the heterogeneity of the chosen architecture may unnecessarily expose private keys to
adversaries.
C. Certain devices are inherently less secure than others, so compensatory controls will be needed to address the delta between device vendors.
D. MDMs typically will not support heterogeneous deployment environments, so multiple MDMs will need to be installed and configured.
CompTIA Security+ Question M-14
In which of the following situations would it be BEST to use a detective control type for mitigation?
A. A company implemented a network load balancer to ensure 99.999% availability of its web application.
B. A company designed a backup solution to increase the chances of restoring services in case of a natural disaster.
C. A company purchased an application-level firewall to isolate traffic between the accounting department and the information technology department.
D. A company purchased an Intrusion Prevention System (IPS) system, but after reviewing the requirements, the appliance was supposed to monitor, not block any traffic.
E. A company purchased liability insurance for flood protection on all capital assets.
CompTIA Security+ Question M-13
The IT department’s on-site developer has been with the team for many years. Each time an application is released, the security team is able to identify multiple vulnerabilities. Which of the following would BEST help the team ensure the application is ready to be released to production?
A. Limit the use of third-party libraries.
B. Prevent data exposure queries.
C. Obfuscate the source code.
D. Submit the application to QA before releasing it.
CompTIA Security+ Question M-12
A cybersecurity analyst needs to implement secure authentication to third-party websites without users’ passwords. Which of the following would be the BEST way to achieve this objective?
A. Open-standard Authorization protocol (OAuth)
B. Single Sign-On (SSO)
C. Security Assertion Markup Language (SAML)
D. Password Authentication Protocol (PAP)
CompTIA Security+ Question M-11
In which of the following risk management strategies would cybersecurity insurance be used?
A. Transference
B. Avoidance
C. Acceptance
D. Mitigation